Table of Contents
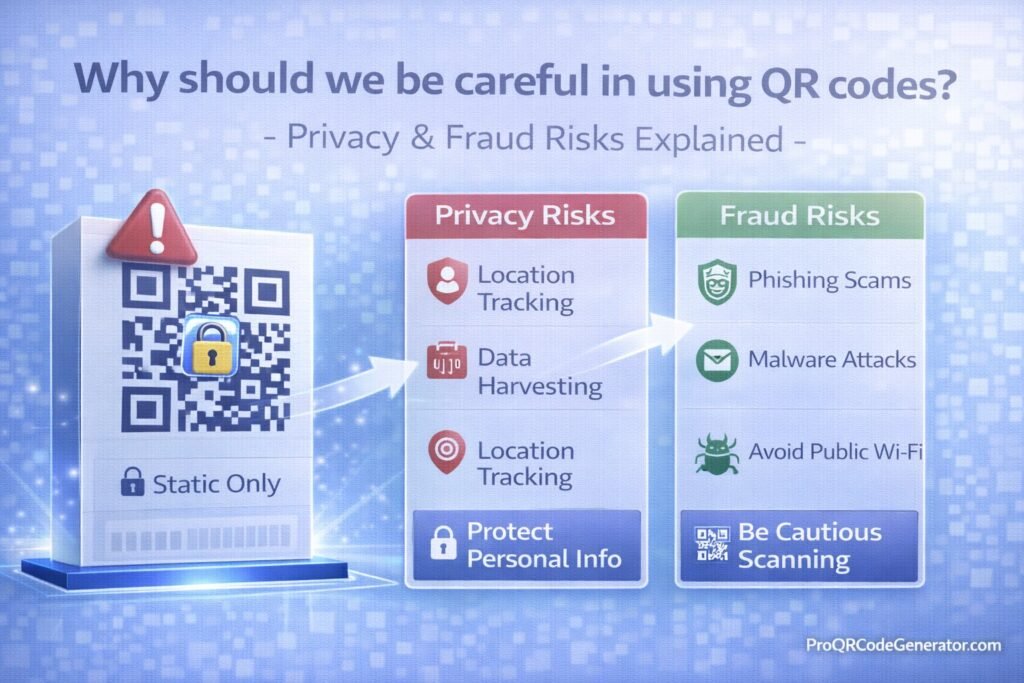
QR codes have transformed how we interact with the digital world. From restaurant menus and product packaging to contactless payments and event check-ins, they offer instant access with a simple scan. Yet as adoption grows, so does the attack surface.
So, why should we be careful in using QR codes? – Privacy & Fraud Risks Explained becomes more than a casual question. It is a security and governance issue for individuals, marketers, and enterprises alike.
QR codes themselves are not inherently dangerous. The risk lies in what they connect to, how they are managed, and how users interact with them. This article breaks down the privacy risks, fraud threats, technical vulnerabilities, and best practices that every user and business should understand.
What Are QR Codes and Why Are They Widely Trusted?
How QR Codes Work
A QR (Quick Response) code is a two-dimensional barcode that stores encoded data. That data may include:
- Website URLs
- PDF downloads
- WiFi credentials
- vCard contact information
- Email templates
- WhatsApp chat links
- Payment addresses
When scanned with a smartphone camera or QR scanner, the device decodes the embedded data and executes an action—often opening a web page automatically.
The core issue: users cannot visually inspect the destination before scanning. Unlike typed URLs, QR codes hide intent.
Why Users Trust QR Codes
QR codes are trusted largely because of context:
- They are placed on official posters or menus
- They appear on product packaging
- They are used in payment systems
- They are endorsed by brands
This physical placement creates psychological trust. Users assume legitimacy because the code exists in a real-world environment. Attackers exploit this assumption.
That is one reason why we should be careful in using QR codes—they combine convenience with opacity.
Privacy Risks of Using QR Codes
While fraud and phishing receive most attention, privacy exposure is equally important.
Hidden Data Collection
When you scan a QR code that leads to a website, the following data can be collected:
- IP address
- Device type
- Browser fingerprint
- Operating system
- Scan timestamp
- Approximate geographic location
Many legitimate marketing campaigns use this data for analytics. However, users are often unaware that scanning a QR code may trigger detailed tracking.
Behavioral Profiling & Analytics Tracking
Advanced QR systems can log:
- Number of scans per user session
- Location heatmaps
- Time-of-day engagement
- Conversion actions
This data is valuable for marketers but raises privacy concerns if:
- Users are not informed
- Data is stored insecurely
- Data is shared with third parties
When businesses use professional dynamic platforms, analytics are typically centralized and protected. For example, structured platforms like ProQRCodeGenerator.com allow businesses to manage scan data securely while maintaining compliance standards.
Device Fingerprinting & Tracking Without Consent
Some malicious or poorly designed landing pages may implement:
- Browser fingerprinting
- Cookie-based tracking
- Retargeting scripts
- Hidden pixel tracking
Even without entering personal data, a user may expose identifiable patterns.
Understanding these risks explains further why we should be careful in using QR codes—they can silently expand your digital footprint.
Compliance & Regulatory Exposure
For businesses deploying QR campaigns, privacy regulations matter:
- GDPR
- CCPA
- Data protection laws
- Payment data standards
If QR codes direct users to unsecured or non-compliant landing pages, the liability shifts to the organization.
QR codes are not just marketing tools—they are data gateways.
Fraud Risks Explained
Beyond privacy, fraud risks represent the most serious threat category.
QR Phishing (Quishing)
“Quishing” refers to phishing delivered via QR codes.
How It Works:
- Attacker generates malicious QR code.
- It redirects to a fake login page.
- Victim enters credentials.
- Credentials are harvested instantly.
Targets commonly include:
- Banking accounts
- Corporate SSO portals
- Cryptocurrency wallets
- Microsoft 365 accounts
Because mobile screens are smaller, users often overlook subtle domain differences.
Payment Redirection Fraud
QR codes are widely used for:
- Restaurant payments
- Parking meters
- Crypto transfers
- Retail checkout
Attackers may:
- Replace legitimate QR codes with stickers
- Redirect payment flows to fraudulent accounts
Once funds are transferred—especially crypto—recovery is extremely difficult.
This financial vulnerability is a central reason why we should be careful in using QR codes in payment environments.
Malware & Drive-By Downloads
Malicious QR codes can redirect users to:
- Fake app download pages
- Trojan APK files (Android)
- Malicious configuration profiles (iOS)
- Exploit-kit websites
Even if installation requires user interaction, social engineering can increase success rates.
Identity Theft & Credential Harvesting
A QR code leading to a fake login portal may capture:
- Email addresses
- Passwords
- Banking details
- Two-factor authentication codes
Once stolen, attackers can:
- Perform account takeover
- Reset passwords
- Execute financial fraud
Real-World QR Code Scam Scenarios
Restaurant Menu Tampering
An attacker places a sticker over the original QR code. Customers scan and enter card details on a fake payment page.
Parking Meter Fraud
Fraudsters attach QR stickers to parking machines, redirecting payments to scam websites.
Corporate Office Attack
Employees receive a flyer with a QR code leading to a fake HR portal requesting login verification.
Crypto Event Scams
QR codes promising airdrops redirect to malicious wallet connection pages.
These scenarios demonstrate the real-world implications of neglecting QR code governance.
Static vs Dynamic QR Codes: Risk Comparison
| Feature | Static QR Code | Dynamic QR Code |
|---|---|---|
| Editable after printing | No | Yes |
| Disable option | No | Yes |
| Scan analytics | No | Yes |
| Redirect control | No | Yes |
| Threat mitigation | None | Immediate |
Static QR codes permanently embed a URL. If that URL becomes compromised, the code cannot be changed.
Dynamic QR codes use a redirect layer. If the destination becomes unsafe, it can be modified instantly without reprinting materials.
Professional platforms such as ProQRCodeGenerator.com provide centralized control, allowing businesses to:
- Update links
- Monitor unusual traffic
- Disable compromised campaigns
- Track suspicious scan patterns
From a risk management standpoint, dynamic QR codes significantly reduce exposure.
How to Use QR Codes Safely (Step-by-Step)
For Individuals
- Preview the URL before opening.
Check domain spelling carefully. - Avoid entering credentials immediately.
If prompted to log in, open the official website manually. - Inspect physical codes.
Look for sticker overlays or tampering. - Avoid sensitive transactions via public QR codes.
Especially banking and crypto transfers. - Keep devices updated.
Security patches prevent exploit vulnerabilities. - Enable multi-factor authentication (MFA).
This reduces the impact of credential theft.
For Businesses
- Use dynamic QR infrastructure.
- Enforce HTTPS on all landing pages.
- Monitor analytics for anomalies.
- Restrict redirect access with role permissions.
- Periodically audit printed materials.
- Avoid linking directly to raw payment processors.
Dynamic systems allow immediate response to suspicious behavior, which is critical in fraud prevention.
QR Code Analytics & Privacy Balance
Analytics are not inherently negative. In fact, they are essential for:
- Campaign performance measurement
- Conversion attribution
- Offline-to-online tracking
- Marketing ROI analysis
However, businesses must:
- Provide transparency
- Secure stored data
- Limit data retention
- Avoid excessive tracking
Platforms like ProQRCodeGenerator.com combine advanced analytics with structured management, helping businesses monitor scans responsibly while maintaining operational control.
ROI vs Risk – Are QR Codes Still Worth It?
Despite the privacy and fraud concerns, QR codes offer measurable value:
- Contactless engagement
- Increased user convenience
- High scan adoption rates
- Direct mobile conversion
- Real-time campaign optimization
The key is not avoiding QR codes—but managing them correctly.
The question is not whether QR codes are dangerous. The question is whether they are deployed responsibly.
Common Mistakes That Increase QR Code Risk
- Using free static QR generators for business campaigns
- Printing codes permanently without backup control
- Ignoring scan analytics
- Linking directly to payment wallets
- Not securing landing pages with HTTPS
- Failing to audit physical signage
These mistakes increase exposure dramatically.
Security Governance Framework for Organizations
For enterprises, QR codes should be treated as managed digital assets.
Recommended governance model:
- Centralized QR management platform
- Role-based access controls
- Redirect approval workflows
- Scan anomaly monitoring
- Scheduled link audits
- Incident response protocol
When managed professionally, QR campaigns become measurable and secure assets rather than unmanaged liabilities.
Why Should We Be Careful in Using QR Codes? – Final Perspective
So, why should we be careful in using QR codes? – Privacy & Fraud Risks Explained?
Because QR codes:
- Conceal destinations
- Can enable phishing
- May redirect payments fraudulently
- Can trigger malware downloads
- Often collect behavioral data
- Expand digital attack surfaces
Yet, when deployed with proper controls, QR codes remain powerful tools for engagement and conversion.
Individuals must practice cautious scanning habits. Businesses must adopt dynamic management, analytics oversight, and security governance.
Solutions like ProQRCodeGenerator.com illustrate how modern QR platforms balance usability, analytics, and risk mitigation without compromising marketing performance.
Convenience should never eliminate caution. With intelligent deployment and structured oversight, QR codes can be both safe and effective.